Cryptology and the Battle of Midway – Emergence of a New Weapon of Warfare
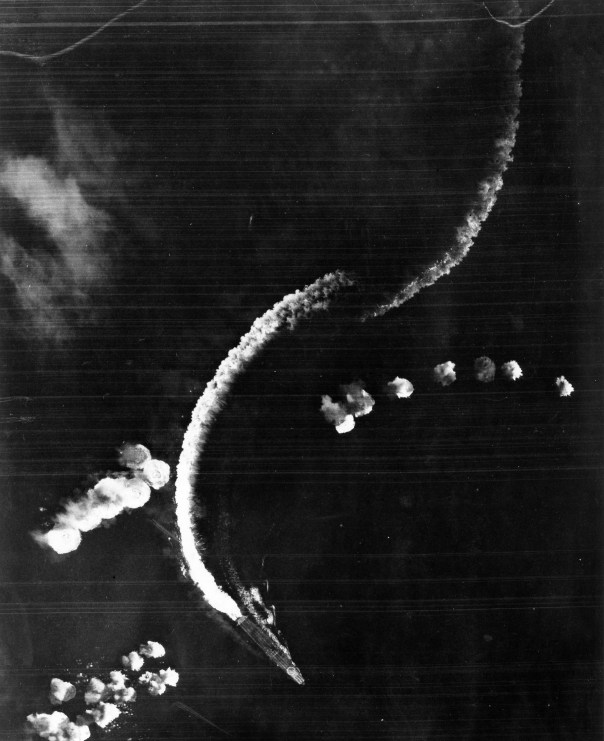
Here the Japanese carrier Hiryu dodges bombs dropped from Midway-based B-17 bombers (source: U.S. Navy).
The outcome of the war hung in the balance. Until now, the United States Navy’s operational effectiveness and readiness was in peril as they had suffered significant losses of the scant few carriers they had in the Pacific Fleet prior to December 7, 1941. The Imperial Japanese naval forces had extended their effective reach to include most of the Western and Southern Pacific and were seeking overall dominance of the ocean. The only opponent standing in their way was the severely weakened U.S. Navy.
In the previous six months, the American Navy had sustained strategic losses near Java with the sinking of the USS Houston (CA-30) in the Sunda Strait and the USS Edsall (DD-219) in the Java Sea, both on March 1.
Looking to put the Japanese on the defensive, American forces struck the Japanese homeland launching a (psychologically) successful air strike from the deck of the USS Hornet, causing Japanese military leadership to start holding back naval and aviation resources as a home guard, reducing the offensive capabilities. Japan had to consider herself vulnerable for the first time in the war while trying to convince citizens otherwise.
Continuing to press their imperial expansion Southward (Australia’s natural resources the ultimate goal), the Japanese, preparing for an offensive to take Port Moresby, New Guinea, began mobilizing the Combined Fleet in the South Pacific. American Forces countered and pressed for an attack which resulted in what came to be known as the Battle of the Coral Sea. While this battle was a strategic win for the United States, it was substantially painful losing the carrier Lexington and sustaining substantial damage to the Yorktown, leaving the Navy with just two serviceable flat tops, Enterprise and Hornet.
The Coral Sea battle demonstrated that over-the-horizon naval warfare had emerged as the new tactic of fighting on the high seas, as the carrier and carrier-based aircraft surpassed the battleship as the premier naval weapon.
While the Navy was very public in developing aviation during the 1920s, behind the scenes, a new, invisible weapon was being explored. Radio communication was in its infancy following World War I and adversarial forces were just beginning to understand the capabilities of sending instantaneous messages over long distances. Simultaneously, opponents were learning how to intercept, decipher and counter these messages giving rise to encryption and cryptology.
Officially launched in July of 1922, Office of Chief Of Naval Operations, 20th Division of the Office of Naval Communications, G Section, Communications Security (or simply, OP-20-G) was formed for the mission of intercepting, decrypting and analyzing naval communications from the navies of (what would become) the Axis powers: Japan, Germany and Italy. By 1928, the Navy had formalized a training program that would provide instruction in reading Japanese Morse code communications transmitted in Kana (Japanese script) at the Navy Department building in Washington D.C. in Room 2646, located on the top floor. The nearly 150 officers and enlisted men who completed the program would come to be known as the “On The Roof Gang” (OTRG).
By 1942, Naval Cryptology was beginning to emerge as a viable tool in discerning the Japanese intentions. The Navy was beginning to leverage the intelligence gathered by the now seasoned cryptanalysts which ultimately was used to halt the Japanese Port Moresby offensive and the ensuing Coral Sea battle. However, the Japanese changed their JN-25 codes leaving the naval intelligence staff at Fleet Radio Unit Pacific (known as Station HYPO), headed by LCDR Joe Rochefort, scrambling to analyze the continuously increasing Japanese radio traffic.
A breakthrough in deciphering the communication came after analysts, having seen considerable traffic regarding objective “AF,” suggested that the Japanese were targeting the navy base at the Midway Atoll, 1,300 miles Northwest of Hawaii. While this information would eventually prove to be
invaluable and was ultimately responsible for placing Pacific Fleet assets in position to deal a crushing blow to the Japanese Navy, it was anything but an absolute, hardened fact. Fleet Admiral Chester Nimitz risked the balance of his carriers (Hornet, Enterprise and Yorktown) sending them to lie in wait of the assumed impending attack.
The attack came and the prepared American forces struck back, inflicting heavy damage to IJN forces, sinking four carriers, one cruiser and eliminating 250 aircraft along with experienced aviators. Though the war would be waged for another three years, the Japanese were never again on the offensive and would be continuously retracting forces toward their homeland. The tide had been turned.
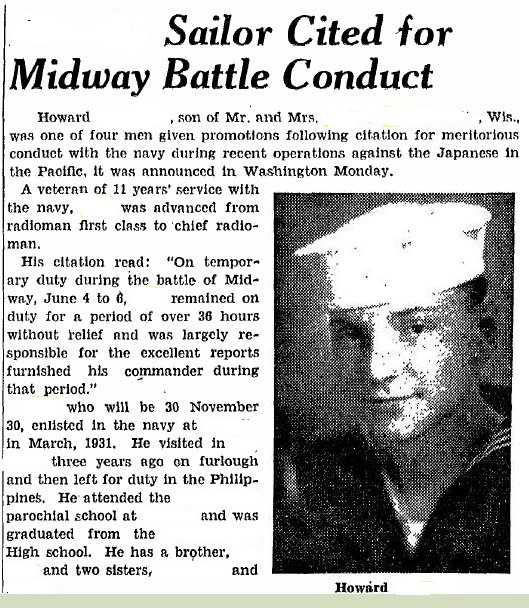
News clipping citing my uncle’s meritorious promotion (one of four sailors advanced for actions during the Midway battle) by Admiral Spruance .
On this 74th anniversary of the Battle of Midway, I wanted to spotlight a different aspect of the history of the battle, the emergence of cryptology as a strategic weapon, and share some of my own collection of that focuses on one of the original OTRG alumni, my uncle Howard.
Howard enlisted as an Apprentice Seaman in the Navy in 1932 (despite what the news clipping states) and proceed to serve in the fleet while working toward a radioman rating. He would be rated as a radioman 3/c in 1934 and accept an assignment to cryptological training at OP-20-G. In the years leading up to the war, he was assigned to Station HYPO and Station CAST (at the Cavite Navy Yard, Philippine Islands) transferring days before the Japanese raid.
- This service record entry shows that my uncle was meritoriously promoted for his actions during the Midway battle.
- This service record entry was also the text of my uncle’s commendation from Admiral Fletcher (acting CTF-16) for providing continuous intel.
Assigned to Station HYPO in early 1942, he would work closely with Commander Rochefort in code-breaking efforts and is purported (in my family circle) to have sent the transmission to Midway personnel to send un-coded messages about their inoperable evaporators, which ultimately led to the confirmation of Midway as Objective “AF.” He would be assigned to the Admiral’s staff (Admiral Raymond Spruance, who was substituting for Halsey at the time) aboard the Enterprise and would receive a meritorious promotion from the admiral as the result of his round-the-clock duties for the duration of the 4-day battle.
- Though these jackets never belonged to my uncle, they represent his achievement – reward for his dedication to duty during the most pivotal naval battle of WWII.
- Assembled from serviceable components from a few WWII navy hats, my dress blue chief radioman display is closer to being complete with this cover.
By 1944, my uncle had been promoted to the officer ranks, making Chief Radio Electrician, warrant officer-1. A career spent in naval cryptology, my uncle retired after 30 years of service.
Regretfully, none of my uncle’s uniforms, decorations or medals survives to this day. Neither of his sons inherited anything from their father’s more than 30 years of naval service. In my decision to honor him, I requested a copy of Uncle Howard’s service record (as thick as an encyclopedia) and began to piece his military tenure together by gathering uniforms and other associated elements. My collection of assembled uniform items representing his career, while not yet complete, has been a long endeavor – dare I say, a labor of love?
Posted on June 6, 2016, in Headwear | Helmets, Rates and Ranks, US Navy, World War II and tagged Admiral Halsey, Admiral Spruance, Battle of Midway, CAST, HYPO, Joe Rochefort, Midway Islands, Objective "AF", On the Roof Gang, OP-20-G, USS Enterprise. Bookmark the permalink. 4 Comments.




Fascinating, I thoroughly enjoyed reading this. What an amazing man.
Greetings,
We are glad that you enjoyed the story. We are very proud of his service and the legacy that he left behind.
Kind regards
What an impressive career he had! You can be very proud of him. Thank you for bringing this information to our attention.
Kit Crissey
Pingback: Airborne Radiomen | The Veteran's Collection